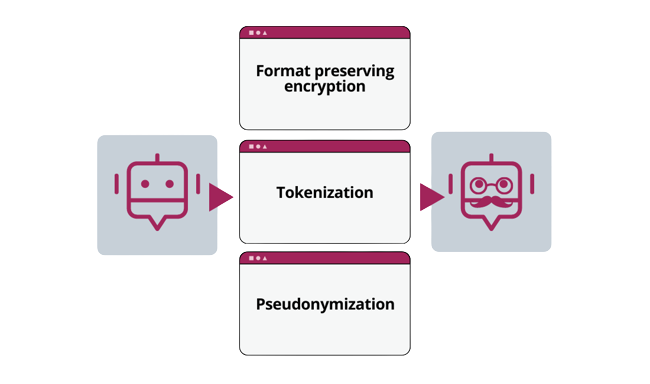
Among the main problems related to the lack of data privacy management we can find:
- High risks of sanctions for non-compliance in the processing of personal data
- Limits on the use of collected data to avoid sanctions
- Reputational risks due to public evidence of misuse of collected personal data